In 2025, internet shutdowns and systemic censorship affected 4.6 billion people more than half of the world’s population. That number is not a projection. It is not a worst case scenario. It is what already happened.
And yet for most people living outside those borders, the reality of what it means to exist behind a government firewall remains abstract. It is worth making it concrete, because what happens to your data in a censored internet environment is not simply about what you cannot see. It is about what the state can see about you.
The Architecture of a Controlled Internet
Government censorship is rarely a single wall. It is a layered system of controls built into the infrastructure that carries your data from your device to the open web. Understanding how those layers work explains why living behind a firewall does not just restrict access — it creates a detailed surveillance record of everything you try to do online.
How Data Flows Differently Under Censorship
In an uncensored network, your data travels from your device to a server through a series of routers that move it toward its destination with minimal inspection. In a censored network, those same routers are equipped with deep packet inspection technology, which reads the contents of your data packets in real time. Governments use techniques including DNS tampering, IP blocking, and keyword filtering to restrict access, and many countries also perform ongoing surveillance of individual users’ web accounts and activity, which can lead to harassment, arrest, or additional oppressive treatment at the hands of government agencies.
This surveillance is not passive. Every search query, every attempt to visit a blocked site, every login to a messaging application passes through infrastructure that is logging what you do. In many firewall environments, that log is accessible to government agencies without a warrant, without notification, and without any meaningful recourse for the individual whose data has been captured.
The Fourteen Year Decline Nobody Is Reversing
Global internet freedom declined for the 15th consecutive year in 2025, as authoritarian governments employed censorship and offline repression to quash protests that were organized online. This is not a trend that has stabilized. According to Freedom House, around 80% of global internet users live in countries that exercise some sort of online censorship or surveillance. That is four in every five people with internet access operating in an environment where their data is monitored, filtered, or both.
The countries with the most severe restrictions share a common characteristic: the firewall is not just a content filter. It is a data collection system dressed up as one.
What Governments Actually Do With Your Data
The data collected through censorship infrastructure serves purposes that go well beyond filtering objectionable content. Many governments mandate that ISPs and telecom organizations retain personal data for extended periods, allowing for retroactive surveillance, and governments are increasingly using AI to detect and censor content more efficiently across large volumes of data.
Surveillance as the Primary Function
In China, the Great Firewall does not simply block Google, Facebook, and Twitter. It routes all traffic through state monitored infrastructure where behavioral patterns are analyzed, flagged, and stored. China has also blocked AI platforms including ChatGPT, Microsoft Copilot, and Hugging Face, while developing domestic alternatives that are required by government frameworks to align with Communist Party positions on sensitive topics.
The practical consequence for individuals is that their digital behavior, the sites they attempted to visit, the searches they ran, the apps they used becomes a permanent record held by a government that can act on it at any time. In environments like this, a single search term can trigger a review of someone’s entire digital history.
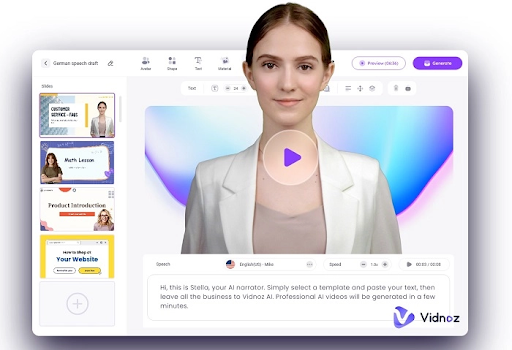
This is exactly why many people living under or traveling through censored networks rely on bypass censorship tools like PureVPN that use obfuscated servers and domain fronting technology to disguise VPN traffic as regular internet activity. When your connection looks like ordinary HTTPS traffic to deep packet inspection systems, it cannot be identified, flagged, or used to build a profile of what you were trying to access.
The Shift Toward More Sophisticated Control
The nature of censorship itself is changing. In 2025, a record 313 internet shutdowns were documented across 52 countries, with seven nations appearing on the list of offenders for the first time. Governments are shifting from total internet blackouts to more targeted restrictions, a trend that reflects both greater technical sophistication and a desire to maintain economic activity while still controlling information flow.
Whitelisting and the New Censorship Model
Both Iran and Russia are now pivoting toward whitelisting, a system that blocks the entire internet by default and allows only a handful of government approved services to function, the inverse of traditional blacklisting. In a whitelisted environment, your data does not escape into an open network at all. Everything you do online is conducted within a closed system where every interaction is visible to the state by design.
This represents a qualitative shift in what censorship means for personal data. In a blacklisted system, data about failed attempts to access restricted content is collected. In a whitelisted system, all data including approved activity flows through state infrastructure. The distinction matters enormously for anyone trying to understand what their digital footprint looks like to the government monitoring it.
Governments in 10 Asian countries imposed 56 new restrictions in 2025, impacting roughly 2 billion people, and social media platforms were the target of one quarter of all restrictions.
For the individuals affected, this means communications conducted through those platforms — messages, posts, account activity were either blocked or rerouted through monitored alternatives.
Protecting Your Data When the Infrastructure Cannot Be Trusted
For people living in or traveling through countries where the internet infrastructure itself is a surveillance tool, the question of data protection becomes a question of basic digital safety. The standard advice around strong passwords and two factor authentication assumes that the underlying network is neutral. In a censored environment, that assumption does not hold.
What changes the picture is encrypting your connection before it enters the monitored infrastructure. Using PureVPN’s servers makes VPN traffic appear as ordinary internet traffic, which prevents deep packet inspection systems from identifying it as a VPN connection and blocking or logging it accordingly. With a verified no logs policy independently audited by KPMG and servers across 78 countries, it gives users in restricted environments a practical route to a connection that does not hand their data to the infrastructure watching it.
The Data Problem Does Not End at the Border
One final reality worth understanding: the data collected under censorship regimes does not always stay within those regimes. Agreements between governments, data sharing arrangements with allied states, and the sale of surveillance technology across borders mean that information collected by one government’s firewall can reach others. For anyone whose digital history exists in a monitored environment, that history does not disappear when they travel or emigrate. It remains, somewhere, in a record that was never meant to protect them.
The firewall was never just about what you cannot access. It has always been about what cannot be kept private.