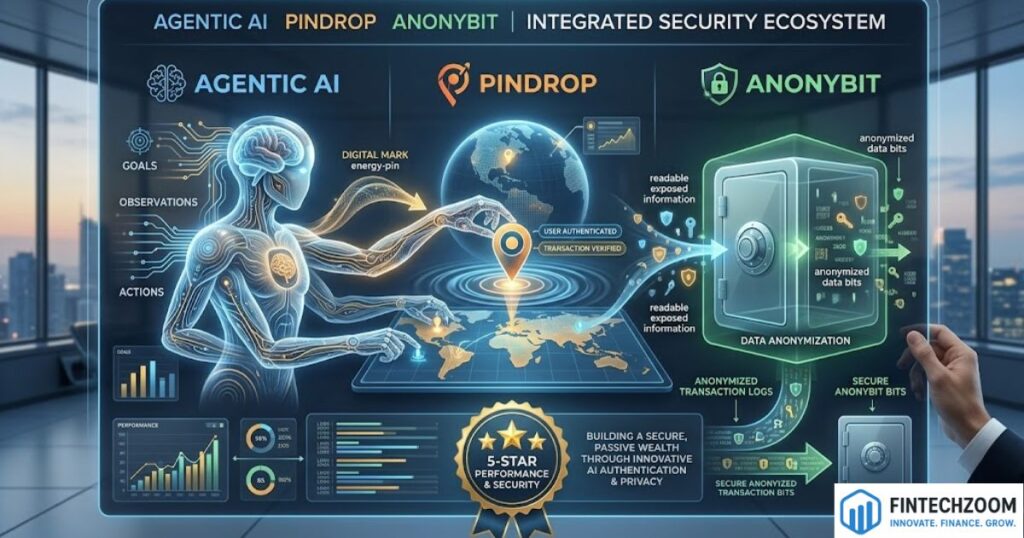
The digital landscape is currently witnessing a massive shift in how organizations approach identity verification. As traditional methods like passwords and two-factor authentication fall victim to sophisticated social engineering and deepfake technology, a new triad of defense has emerged. The combination of agentic ai pindrop anonybit represents a move toward autonomous, self-healing security ecosystems. This framework does not just flag risks; it acts upon them in real time, ensuring that unauthorized access is blocked before a human administrator even notices the attempt.
The Rise of Autonomous Decision Making in Identity
Modern security is moving away from static rules that require manual intervention. In an era where cyberattacks happen at machine speed, waiting for a human to review a suspicious login is no longer viable. Autonomous systems are now being deployed to handle high-volume authentication tasks with incredible precision. These systems observe behavioral patterns, cross-reference them with historical data, and make independent decisions to allow or deny access. By integrating these capabilities into the identity stack, businesses can maintain a “zero trust” environment where every interaction is continuously verified without slowing down the legitimate user experience.
Transforming Voice Verification for the Modern Age
Voice has long been a vulnerable vector for fraudsters, particularly with the advent of high-quality voice cloning tools. Advanced audio analysis now allows platforms to distinguish between a live human lung pushing air and a synthetic recording or a speaker-generated imitation. This process happens in the background of a call, analyzing over 250 vocal characteristics in milliseconds. By focusing on the “liveness” of the sound, organizations can protect their contact centers from account takeover attacks that specifically target the phone channel. This transition from simple recognition to deep liveness detection is essential for industries like banking and healthcare.
Securing Biometric Data through Decentralization
One of the greatest risks in digital identity is the centralized storage of biometric data. If a database containing fingerprints or facial scans is breached, that data is permanently compromised. To solve this, a decentralized approach is now being used to break biometric information into tiny, encrypted fragments. These fragments are stored across a distributed network, making it impossible for a hacker to reconstruct a usable biometric profile from a single point of failure. This method ensures that even if a part of the system is compromised, the actual identity of the user remains shielded and unreadable to unauthorized parties.
Real Time Defense Against Synthetic Media Threats
The surge in deepfake technology has made it difficult to trust any digital interaction. Synthetic voices and faces can now bypass many standard security checks. However, by layering multiple forms of verification, such as voice biometrics and decentralized identity checks, companies can create a defense that is nearly impossible to crack. When a high-value transaction is initiated, the system can simultaneously verify the voice, check the biometric integrity, and analyze the behavioral context such as the device being used and the geographic location to ensure a complete match before proceeding with the request.
Reducing Operational Friction in Contact Centers
Customer service environments often struggle to balance security with speed. Legacy authentication methods, such as asking knowledge-based questions about a user’s first pet or street name, add minutes to every call and frustrate customers. Modern integrated solutions can reduce authentication times by over 60%, often verifying a user’s identity in under five seconds. This is achieved by performing passive checks while the customer is speaking naturally to an IVR system or a live agent. The result is a significant reduction in average handle time and a massive boost in customer satisfaction scores across the board.
Navigating the Complexities of Global Privacy Laws
Compliance with regulations like GDPR and CCPA has become a top priority for global enterprises. Handling sensitive biometric data requires a high level of transparency and security. The use of zero-knowledge architectures allows organizations to verify identities without ever actually “seeing” or “storing” the raw biometric data in a traditional sense. This aligns perfectly with privacy-by-design principles, allowing businesses to meet stringent regulatory requirements while providing a high level of security. Automated audit trails also ensure that every autonomous action taken by the security system is logged for future review.
Scaling Security for the Future Digital Workforce
As organizations adopt more AI-driven tools, the definition of the “workforce” is expanding to include non-human identities. These autonomous agents need their own sets of credentials and access permissions. Managing these identities at scale requires a robust framework that can handle thousands of concurrent interactions. By applying the same rigorous biometric and behavioral standards to these digital employees, companies can prevent “shadow AI” risks and ensure that every action taken within their network whether by a human or a machine is fully authenticated and authorized.
Security Performance Metrics
| Metric Category | Traditional Methods | Integrated AI Defense |
| Authentication Speed | 45 – 90 Seconds | < 10 Seconds |
| Fraud Reduction Rate | 30% – 40% | > 80% |
| Reliance on Passwords | 100% | 0% (Passwordless) |
| Deepfake Detection | Manual/Low Accuracy | > 99% Accuracy |
| Data Storage Risk | High (Centralized) | Minimal (Decentralized) |
FAQs
How does this framework prevent voice cloning?
The system uses liveness detection to analyze the physical properties of the sound. It can detect the lack of natural speech variations or the presence of digital artifacts that are common in synthetic audio, even if the voice sounds identical to a human ear.
Is biometric data stored on a central server?
No, the decentralized approach ensures that biometric data is fragmented and encrypted across multiple locations. No single “key” or image of the user is ever stored in one place, which protects against large-scale data breaches.
Does this technology slow down the user experience?
Actually, it speeds it up. Because the verification happens passively in the background (such as while you are talking to a representative), there is no need to stop and answer security questions, making the process much smoother.
Can it detect deepfakes in real-time meetings?
Yes, the latest integrations allow for continuous monitoring during virtual meetings. If an unauthorized “imposter” or a synthetic video feed is detected, the system can immediately alert the participants or terminate the session.
Conclusion
The convergence of agentic ai pindrop anonybit represents the next logical step in the evolution of cybersecurity. By moving away from reactive, human-dependent security and toward an autonomous, decentralized, and multi-layered model, organizations can finally stay ahead of modern threat actors. This approach not only hardens the defense against deepfakes and data breaches but also removes the friction that has plagued user authentication for decades. As we move further into 2026, the ability to act with machine-level speed and biometric certainty will become the standard for any business operating in a high-risk digital environment. The focus is no longer just on identifying a threat, but on providing a system that can think, reason, and defend itself independently.